(Last update: 19 January 2024)
If you are considering applying to the
Master's Degree in Computer Science program at UPLB, here are some things you might want to know
based on my experience and observations.
Who should take this degree program?
"The Master of Science in Computer Science (MSCS) degree program addresses the need for advanced formal training of professional leaders in Computer Science. Candidates are expected to acquire a broad knowledge of the discipline and be able to undertake critical inquiry and independent research."
This program is ideal for those who want to become professors or researchers. The MSCS program can also be treated as a 'bridge' program if you want to get into a PhD program. If you are an industry practitioner, you might want to take the
Master of Information Technology(MIT) program (non-thesis) instead. As much as possible, you should have
good grades during undergrad to increase your chances of getting accepted and completing the regular program.
What prerequisite knowledge is required?
This program requires that you've completed a
BSCS/BSIT/BSIS program from a 'recognized' HEI. Here are some of the courses you should have good grades in (2.0 or better).
* Discrete Mathematics
* Statistics
* Data Structures and Algorithms
* Programming Languages
* Databases
* Operating Systems
* Computer Networks
* Automata and Language Theory
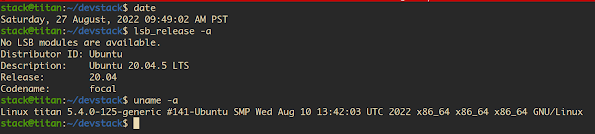
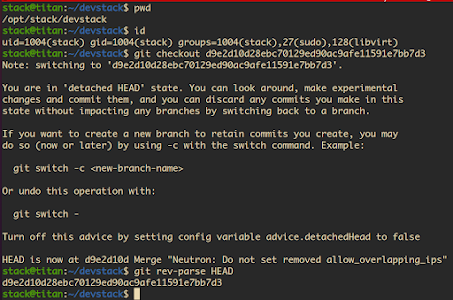
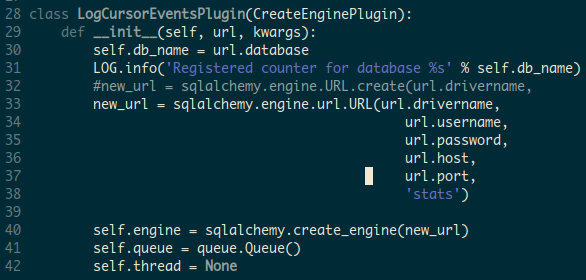
You should also be proficient in programming. Web programming is a must if you plan to minor in IT.
Being proficient in Linux and Python is a plus.
If you are interested to join our group, I prefer students who have good background in machine organization/architecture and low-level programming (assembly and C), operating systems admin/internals, and computer networks.
Program requirements
The program requires at least 34 units to complete, divided into the following.
* Core Courses (12 units) - required
- Programming Languages, Advanced Computer Systems, Advanced Data Structures and Algorithms, Computational Complexity Theory
* Major Courses (6 units) - select two(2) from the following courses
- Databases, Automata and Language Theory, Scientific Computing, Digital Image Processing, Management Information Systems, Parallel Processing, Special Topics
* Minor Courses (9 units) - select three(3) courses from one of the following graduate programs
- Mathematics, Statistics, Economics, Agriculture, Forestry, Information Technology, Environmental Science
* Seminar (1 unit)
* MS Thesis (6 units)
In addition to passing the courses above (with a grade of 2.0 or higher), you also need to pass the Comprehensive Exam.
Who are the professors currently teaching the graduate CS/IT courses?
(as of Academic Year 2023-2024)
* Patrick Albacea (Programming Languages, Operating Systems)
* Fermin Roberto G. Lapitan (Web App Dev)
* Marie Art Antonette Clarino (Modeling and Simulation, Data Structures, Algorithms)
* Joseph Anthony Hermocilla (Cybersecurity, Modern Distributed Systems)
* Concepcion Khan (Information Systems, Knowledge Management)
* Val Randolf Madrid (AI/ML, Machine Vision)
* Danilo Mercado (Enterprise Systems, Cybersecurity)
* Jaderick Pabico (AI/ML, Parallel Programming)
* Reginald Recario (Databases)
* Jaime Samaniego (Data Structures, Algorithms, Computational Complexity Theory, Automata)
Part-time or full-time mode?
If your home institution, funding institution, or employer will allow it, choose full-time. The advantage of full-time mode is that you can focus on the coursework and still have plenty of time to research.
Choosing your adviser/supervisor
Use your first semester, or even before applying to the program, to scout for a suitable adviser. Ask other students. Visit research group websites of professors. Check the publications of professors. Attend talks. Talk directly to a possible adviser via email or in person.
Note that you will be assigned a temporary registration adviser upon admission to handle enrolment/registration matters. If a professor has accepted you as advisee even before admission, then he/she will automatically be your registration adviser.
Choosing your adviser is a tricky task. The following are some guidelines on how to select an adviser (based on my opinion).
* Choose an adviser who 'specializes' in the area that you are interested in.
You want an adviser who can guide you in your research. Some advisers are generalists, but choosing a specialist is best.
* Choose an adviser who is 'easy to work with.'
Some advisers can be challenging to work with. Some are too intimidating and too demanding with unreasonable expectations. Some are not even available for regular consultations.
* Choose an adviser who has connections outside of ICS or UPLB.
If your adviser is active and visible in the research/scientific community, it will enlarge your network and open up opportunities for collaboration. Some advisers are also involved in externally-funded projects, which can be a good source of a thesis topic.
* Choose an adviser who is ethical.
Your reputation will also be affected if your adviser is involved in unethical research/publication practices.
You also need to select 2-3 professors who will be part your Guidance Committee, with one member from your chosen minor field.
Choosing your minor
Most students choose Information Technology(IT) as their minor. However, it is actually up to you, based on the research area that you want to pursue. For example, a Forestry, Environmental Science, or Economics minor is best if you are interested in Modeling and Simulation or Machine Vision. A Statistics or Mathematics minor will be excellent for a Data Science or AI/ML track.
How are the classes conducted?
Lectures and assignments make up most of the classes. Some IT courses have a separate laboratory class. Unlike in undergrad, reading research papers and writing reviews are incorporated into the class activities. I often hear current students complain about too much readings in their classes. Do not apply to this program if you do not like reading and reviewing research papers. Individual/group programming projects and reporting are required in some courses. A midterm exam and a final exam are also used for assessment. Remember that you need to get a grade of 2.0 or higher. Unlike in undergrad, you must be motivated to study independently and not depend on the professor. Some professors don't give lectures at all and only assign readings and programming assignments.
What are other skills you need to develop?
You will need to develop the following:
* Oral and written communication skills, especially scientific/technical writing
* Critical reading of research papers and writing reviews - one way to do this is by maintaining a blog
* Reporting and presentation skills
* Learning new tech stacks and programming languages
* LaTeX
Another important skill that you need to develop is networking or in general socialization. In addition to your adviser, you need a kind of support group where you can bounce off your ideas and not feel alone.
Comprehensive Exam
Once you've completed the coursework, you will take the Comprehensive Exam. The exam will cover the following areas: Theory, Systems(my specialization), and Applications. Questions will come from professors who taught or specialize in the particular area.
Your first semester
You should spend your first semester to familiarize yourself to the graduate school environment. You will take at least two core courses during your first semester of first year: Advanced Computer Systems (CMSC 215) and Advanced Data Structures and Algorithms (CMSC 244). If you are a full time student, you can take additional courses (up to 12 units). As mentioned above, scout for a possible adviser during your first semester. Also choose your minor and look for Guidance Committee members. I recommend that you attend a research methods class even if it is not required to develop your research skills.
How long will it take to finish?
It usually takes 3-4 years to complete the program, especially for part-time students. Sometimes it will take longer because of the thesis (I will have a separate post to discuss it). That is why I recommend the full-time mode. The UPLB Graduate School has a proposed 'optimistic' timeline below. This timeline may be possible in other disciplines. However, this is quite difficult to achieve in MSCS.
Facilities and resources for students
We have a shared
GS Room where graduate students can stay and work. There are iMacs available, but bringing your own laptop/device is better. Some professors have their own lab space where you can work if they are your adviser. Our main graduate teaching laboratory is
PC Lab 1, with 16 Ubuntu boxes. We have a few servers for running compute-intensive tasks. The
UPLB Main Library has access to a wide collection of research resources, including those published by
ACM and
IEEE. Technical reports from ICS are available at
Peak-One.
How to fund your study?
The tuition fee is currently PHP 1000.00/unit. For the tuition fee alone, you will need at least PHP 34,000.00! If you have enough money, you can fund your study on your own. You can also avail of financial assistance.
Additional information
Closing Thoughts
Be sure that you really need/want the MSCS degree!! If you did not finish your undergrad from UP, you might be 'shocked' by the academic environment here. You need to spend some time adjusting and focusing. Your classmates will probably be instructors from ICS, and they will be really good in your classes. Do not be intimidated by them. Just do your best and excel.
Most of them are friendly and fun to work with in
group projects. Choose your major adviser and Guidance Committee wisely. In Part 2, I will talk about the thesis, research, and publications.
(Photo by Unseen Studio on Unsplash)